Quick Links
Search
© 2023 Shoppersvila. All Rights Reserved.
Volleyball Fans Devastated as Haikyuu!! Season 5 Looks Unlikely Due to New Movie Finale
Volleyball anime fans have been left heartbroken by recent news that a fifth season of…
Is Tayo Ricci Secretly Gay? He Gave the Answer what Everyone’s Asking
Tayo Ricci, the popular social media influencer and singer, has amassed a huge following thanks…
Don't Miss
Is Vijay All Set to Take a Break for Three Years from Acting?
The much-awaited film "Leo" featuring Vijay and Trisha is receiving an overwhelming response from the…
Hollywood
Explore This Category
Is Meri Brown Currently in a New Relationship? Know Who is Meri Dating Now?
Meri Brown was part of a polygamist family for over 30 years as the first…
Who are Milo Manheim’s Real Parents? Uncovering His Unique Family Story
Milo Manheim skyrocketed to fame starring as Zed in Disney Channel's hit movie series Zombies.…
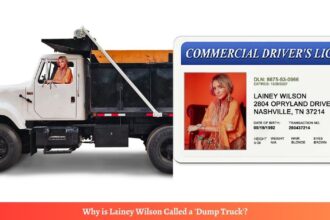
Why is Lainey Wilson Called a ‘Dump Truck’?
15 Min Read
Bollywood
Explore This Category
Adventure
Explore This Category
What Happened to Popular YouTuber TTF Vasan? Is he Alive?
Popular Tamil YouTube star TTF Vasan has been critically injured in a horrific bike accident…
Who is the No. 1 Motovlogger in Tamil Nadu?
Tamil Nadu has a thriving community of talented motovloggers. But one star stands out from…
Top 10 Most Daring Motovloggers in Tamil Nadu
Tamil Nadu's motovlogging scene is thriving, with talented content creators taking to two wheels to…
Who is TTF Vasan? Has TTF Vasan (Twin Throttlers) Died in a Bike Accident?
TTF Vasan, the wildly popular Tamil YouTube motovlogger renowned for his death-defying bike stunt videos…
Stay Connected
Discover Categories
Discover More of What Matters to You:
First AI vs Human Pilot Dogfight: Who Won the AIR Battle?
The US Air Force made history with the first-ever combat test between an AI-controlled aircraft and a human pilot. Conducted…
Here is Why Powerball Winning Numbers Trending in 2024
The year 2024 has seen an unprecedented level of public interest and social media engagement around Powerball winning numbers. With…
Created These Stunning Mother and Baby Unicorn AI Images with DALL-E 3
These breathtaking images were generated using the latest version of DALL-E 3.0, a cutting-edge AI image creation tool that has…
Anushka Sharma Returns Home: Son’s Privacy Prioritized
After a brief absence, Bollywood star Anushka Sharma has returned to India with her newborn son Akaay, making a notable…
A Diamond in the Rough: Finding Samurai in Aladdin?
Disney's animated classic "Aladdin" whisks us away to a vibrant tapestry of Arabian nights, filled with magic, adventure, and romance.…
21 Savage Accused of Scamming Adin Ross With Marked Cards
Rapper 21 Savage is facing backlash after being accused of cheating popular Twitch streamer Adin Ross with marked cards during…
Quaden Bayles Controversy on Bullying Scam: Know the Story
In February 2020, a heartbreaking video of 9-year-old Quaden Bayles went viral globally, bringing attention to the devastating impacts of…